SUMMARY
This is AI generated summarization, which may have errors. For context, always refer to the full article.

MANILA, Philippines (UPDATED) – Two weeks ago, the Duterte Cyber Warriors (DCW) Facebook page released photos of a “mobile offensive tool”, a stingray device that could reportedly monitor Wi-Fi and cellphone traffic within tens of feet to disrupt the communication of people joining the anti-Marcos rally on November 25.
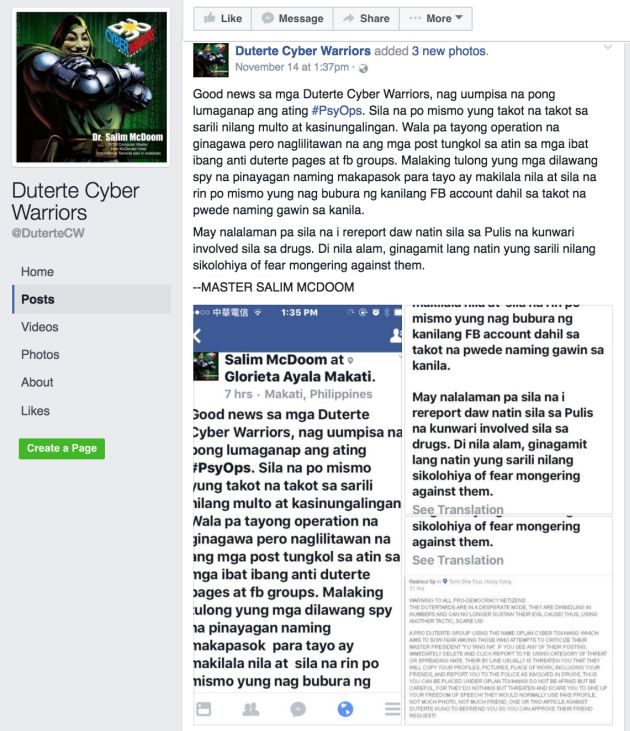
On November 14, the group announced they were engaging in psychological operations or psy ops.
Two days after, DCW called on their followers to be “field operatives” and to buy parts of a “mobile offensive tool kit” for an estimated price of P5,000 to build the device.
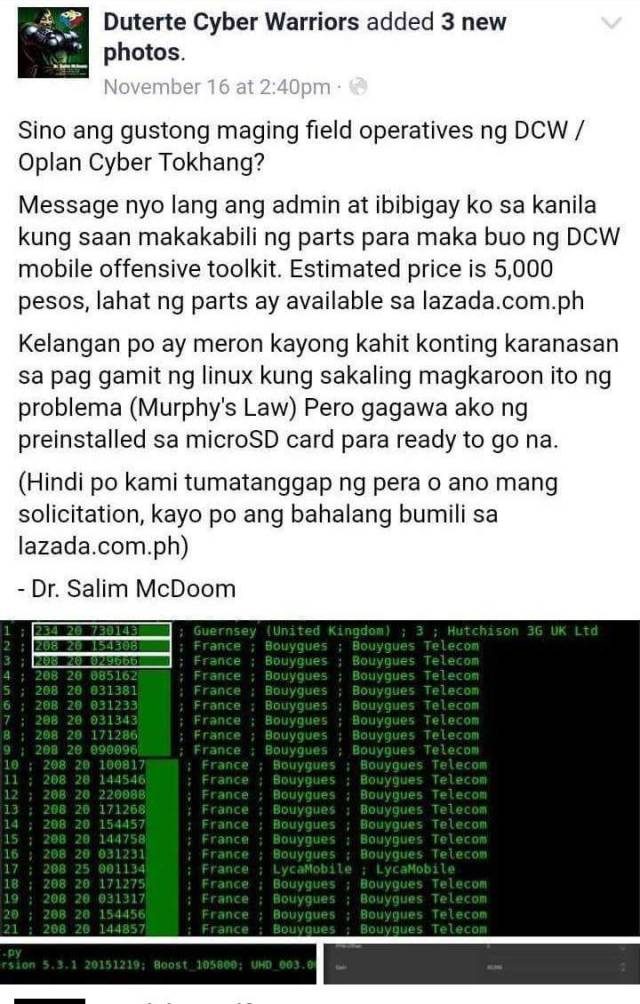
On the same day, they hinted at what they called a “stingray” device.
On November 19, the page released photos of a D-I-Y (do-it-yourself) stingray device that they referred to as the “mobile offensive tool.”
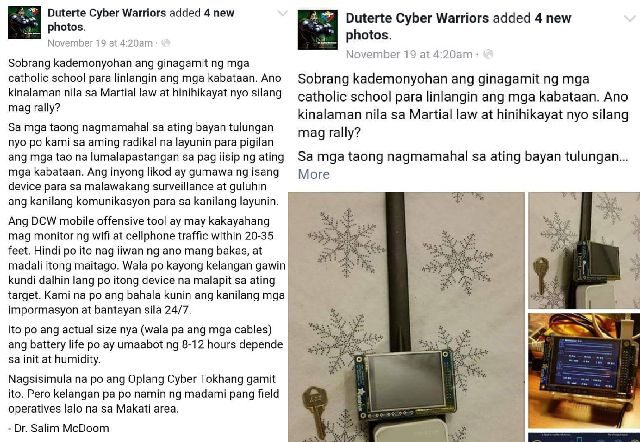
The post said that all that operatives have to do is to approach a target and then DCW would handle the rest, which supposedly includes getting information from the person and monitoring his or her activities.
It was perceived by many as a threat to their privacy, if not the security of their online accounts.
Read more:
Sowing intrigue
More than a week had passed since they announced the existence of this so-called device but it still wasn’t creating the buzz they wanted it to make.
In a chat interview, DCW’s main tech guy Salim McDoom (a pseudonym), often referred to as “Master” or “Doctor” by the group, related the story to Rappler.
McDoom said they monitored the “Cyber Tokhang” conversation online, building a script that automatically searches the term. “We were watching how it would spread.”
The term “Oplan Cyber Tokhang” (OCT) is inspired by the Philippine National Police’s Oplan TokHang, where cops knock on the doors of suspected drug users and dealers.
“TokHang” is a contraction of the Visayan words “toktok” (knock) and “hangyo” (request). Despite the similarity in names, OCT is neither affiliated nor an online counterpart of the government’s Oplan TokHang. (READ: Oplan Cyber Tokhang on Facebook: ‘Extrajudicial reporting’)
A few days before the November 25 rally, several Facebook users were locked out of their accounts. Speculations surfaced about what caused it, including the possibility of a group intending to hack or take down their accounts.
Due to a public callout for “social media war” by DCW the week prior to the incident, some people were quick to point fingers at them. DCW saw this as an opportunity. It was “a nice coincidence,” McDoom said.
“It wasn’t being discussed in any IT/infosec forums yet” until the news of the Facebook lockouts came about. DCW saw how the term began to spread in the Ateneo community so they decided to ride the wave.
On their Facebook page, DCW checked into Katipunan Avenue on November 25 – this is where the Ateneo de Manila University is located – and posted this message to “intrigue” the community there.
McDoom described that post as “cryptic”, adding that they “were careful not to claim responsibility for any hacking.”
That post generated about 25 comments, including: “Cyber terrorism is punishable by law, sirs. You better tread carefully” and “You’ve crossed the line”.
The motive to sow intrigue became successful.
“The main purpose was to get their attention as quick as possible so they can spread our fabricated story,” he said.
McDoom said their announcement about a hacking “device” was necessary because mass reporting alone would not make such a big impact because anyone can do it. “In reality, no one would post their criminal intent,” he added.
Facebook echo chamber
In an email to Rappler on November 28, Facebook took responsibility for the lockouts, saying it was caused by a bug in their system that detects when an account is compromised.
But this explanation does not adequately cover other lockouts caused by other users asking Facebook to review accounts and pages that were allegedly violating Facebook community standards, when this was actually not the case.
McDoom admitted they resorted to “mass reporting”, saying it is “a good exercise” for their community “to vent their frustrations.”
“We encourage them to report posts inciting sedition, but Facebook still has the authority [to determine] which post goes against their community guidelines,” he added. He also said it is the DCW administrators who identify posts that can be classified as “inciting sedition.”
On November 30, Leollard Riyoh, a staunch supporter of Philippine President Rodrigo Duterte who also coined the name “Duterte Cyber Warriors”, released a video blaming “anti-Marcos and anti-Duterte” followers for taking down their Facebook group.
“Akala nila hina-hack natin sila,” he said. (They thought we’re hacking them.) He then went on to say they lied about the stingray device to “manipulate” and condition the minds of people into feeling scared.
It was Riyoh too who, in a video, called for volunteers – giving special mention to Information Technology (IT) experts and programmers – to join a social media civil war they referred to as “Oplan Cyber Tokhang” against the so-called “Yellow Army”.
In an interview with Rappler, DCW said that all the videos that Riyoh posted related to OCT and DCW were part of their psy ops to trick “biased media” and expose their vulnerability when they write reports “without fact checking.”
The group also claimed that their IT volunteers did not and will not engage in any hacking activity and that they are only needed to “analyze critically and professionally” data from what they perceive to be “incorrect” posts of the media. Rappler is not exempted from the list, they said.
“Facebook has an algorithm that creates echo chambers and they designed it this way because tribalism is embedded in our DNA,” McDoom said.
While several have written about the dangers in social media echo chambers over the past year, McDoom thinks there is value in them.
“Magiging magulo ang social media kung di mako-contain yung mga views and opinions in separate channels,” he said. (Social Media will be chaotic if we can’t contain views and opinions in separate channels.)
Stingray device and NTC permit
In theory, the existence of DCW’s stringray device can spoof a cell site, thereby making nearby cell phones vulnerable to hacks.
“I wouldn’t be surprised at all if some unscrupulous person/s have already been doing this out there,” said engineer Pierre Tito Galla, co-founder of cybersecurity watchdog group Democracy.Net.PH.
A source from the telco industry, who requested anonymity and is familiar with the issue, said he is not sure if their cell towers are safe from an attack like that, but if such device is legitimate, it should have a permit from the National Telecommunications Commission (NTC).
There’s a way of going around it, however.
“Any device that has a transmit/receive capablity via radio frequency (RF) emissions requires NTC-type approval but since DCW’s device is ‘homebrew’ from parts that can be sourced legally, and are not illegal in and of themselves, the device avoids being inspected by NTC,” Galla explained.
NTC Commissioner Gamaliel Cordoba told Rappler that they have not authorized the device. “I don’t know about homebrewing such device, but it has to pass through our licensing.”
Anyone who will engage in illegal wiretapping or hacking will be punished under the Republic Act (RA) 9292 or the the Electronics Engineering Law of 2004, he continued.
The stringray showed by DCW is an International Mobile Subscriber Identity (IMSI) catcher and can be made using programmable microprocessors or micro-controllers such as Arduino, Raspberry Pi boards, and wireless routers, all of which can be ordered online and shipped straight to your door.
“Anyone can assemble the device,” DCW said. Several information technology (IT) and computer experts, whom we approached, agreed and said the device is easy to put together.
The difficulty for most people lies in writing the code and converting whatever machine-encrypted data they gather into human readable data. Most codes for these purposes, however, can be copy-pasted from the web and various developers’ forums, Galla said.
It can obtain details like your cellphone number, the hardware, the regular SMS, and phone calls. They could snoop, but secured apps, such as those used by more modern media sites, will not be affected because they are encrypted, explained a veteran computer engineer who also requested anonymity.
They can trace the transmissions but they can’t pretend to be you, which is the point of hacking.
Rappler developer Emmanuel Santiago, an information technologist, and Rappler photojournalist Martin San Diego, a computer science graduate, both think it’s possible to hack with the help of the DCW stingray device but believe there are easier ways to achieve a goal like that.
They cited social engineering as an example, which involves tricking people into breaking normal security procedures such as phishing, tailgating, and many more.
Cybersecurity above all
“This social experiment is one way to educate anyone using the Internet to secure themselves,” DCW said.
Whether any of the cyber attacks you hear are true or not, it’s always best to stay safe.
Ways to protect yourself from these types of attacks include:
- securing your wireless network
- making sure you’re using encrypted and secured sites and apps
- using unique passwords
- installing a trusted security software
- simply being careful with emails
How does this make you feel? Vote on the Mood Meter or write about it on X. – with reports from Chrisee Dela Paz/Rappler.com
Add a comment
How does this make you feel?
There are no comments yet. Add your comment to start the conversation.