SUMMARY
This is AI generated summarization, which may have errors. For context, always refer to the full article.

MANILA, Philippines – On November 12, the Senate approved Senate Bill No. 1030. This bill requires qualified voters to register for voting through biometrics.
According to Sen Aquilino Pimentel III, the implementation of biometrics “will allow a thorough cleansing of the national voters’ registry that will reduce, if not eliminate, cheating.” It attempts to ensure election results “are reflective of the genuine will of the people.”
As much as anyone would want to support a lofty goal such as this, there are issues that Filipinos need to ask about the technology behind it and the bill’s implementation if it is to successfully create meaningful change in the electoral process.
Senate Bill No. 1030 means well. Written by Sen Lito Lapid, the bill’s intent is to cut a swath through incidents of electoral fraud and cheating.
According to the press release, this is done by requiring registered voters to have their “photographs, fingerprints, signatures and other identifiable features” captured and stored as digital data by election officers at one’s place of registration using the data capturing machines of the Commission on Elections (Comelec).
If a registered voter fails to submit his biometric data for future national and local elections, such as those in 2016, he will get cut off the registration record of voters by the Election Registration Board (ERB).
If one has been deactivated from the registration record, that person can apply for reactivation after undergoing the biometric scanning process at the ERB.
Wrong premise
During his sponsorship speech, Senator Pimentel said the Committee on Electoral Reforms and People’s Participation can ensure the Automated Fingerprint Identification System (AFIS) will weed out double or multiple registrants.
One major issue with this is the premise that data is just data, and the acquisition of a large amount of data is not the answer to a problem, especially if the means of acquiring, storing, and using that data is not secure.
Take fingerprints, for example. Google searches for information on fingerprint hacking led to an article on CNN discussing the hacking of biometric information, specifically iris scans. In that article, however, is a paragraph about researchers at the University of Bologna and their reconstruction of fingerprints from digital data.
The article states, “They were so successful that they were able to build gummy finger versions of the prints that could be pressed up against a reader and used to fool the computer into letting them into someone else’s account.”
The University of Bologna appears to have a full research laboratory devoted to biometric systems, and their studies include a long list of activities related to the study of fingerprint recognition, generation, and falsification. They also study other types of biometrics, from faces to signatures, and biometric encryption.
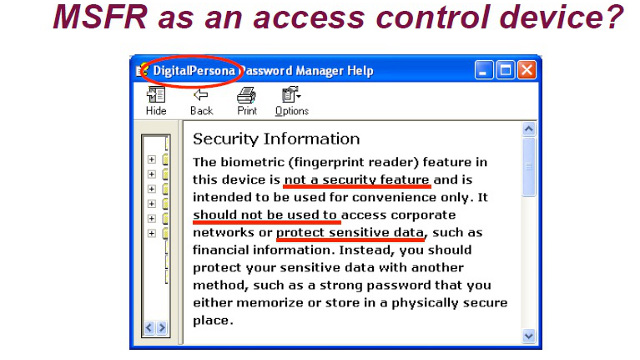
In addition to looking at the science of hacking the biometrics, you also have to worry about the tech. In the Google search for fingerprint hacks was a PDF file link from the 2006 Black Hat conference presentation by Mikko Kiviharju regarding hacking fingerprint scanners, such as Microsoft’s Fingerprint Reader.
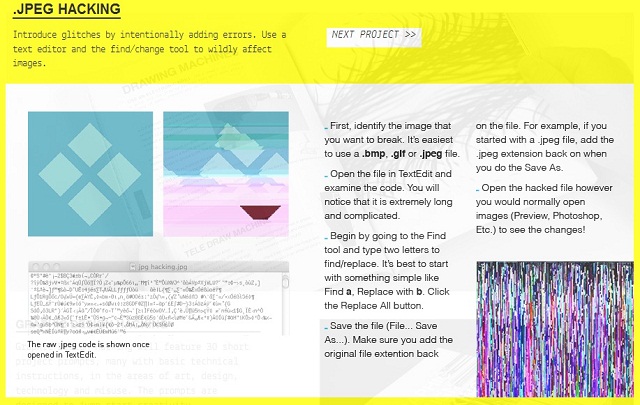
One does not even need to manipulate data severely to create a large impact. If the aim is simply to corrupt data, all one would have to do is open the image file containing the pictures of registered voters in a decent text editor (because visual data can be represented as text code), use the replace function to switch a set of letters in the now-exposed code for the image, and then save it as an image file again. The result is a corrupted image with the same file name, as shown in this web page.
The human element
In addition to concerns about data, one also has to look at the human element of the elections.
While we’ve worried about election violence, coercion, vote buying, and other human agents interfering with elections in the past, we now have to add another wrinkle: the human elements who have access to the data.
There appears to be at least one notable case of information theft with regard to biometric data. According to the Fast Company website, a contract worker with the Israeli Welfare Ministry was accused of stealing Israel’s primary national biometric database back in 2006. He accessed all this information from the relative privacy and comfort of his office. When he was relieved of his position for other offenses, he began sharing it with the Jewish underworld.
The report notes that “the stolen database contained the name, date of birth, national identification number, and family members of 9 million Israelis, living and dead.” Information on birth parents of hundreds of thousands of adopted Israelis and health details of citizens was also in the stolen data.
All this private data first got passed around among a small group of people. It eventually made its way online. So long as someone has this data available to them, it will probably remain online for the foreseeable future.
The idea that any sufficiently malicious person with access to the right skills and technology can wreak havoc to digital data should make politicians pause. Hackers have done it repeatedly with websites of the Philippine government, and potential crisis scenarios of this sort should be taken into account before making decisions of value to the nation.
More importantly, it should make voters ask questions about the specifics of a bill that directly affects their ability to vote and the planned implementation of this system. – Rappler.com
Add a comment
How does this make you feel?
There are no comments yet. Add your comment to start the conversation.