SUMMARY
This is AI generated summarization, which may have errors. For context, always refer to the full article.

MANILA, Philippines — As systems go digital and more high-tech, businesses and organizations around the world have become more vulnerable to cyberattacks.
Businesses in the Philippines are even more at risk. Microsoft ranked PH as the 8th most vulnerable country to malware across the Asia Pacific, and the 10th most attacked country on the internet worldwide according to FBI.
As if these statistics aren’t alarming enough, there are only 84 Filipino Certified Information System Security Professionals and half of them are working overseas.
The Philippines is now more vulnerable than ever and the burden is on business leaders and decision-makers. Fortunately, there are ways to protect yourself and your business. One is by looking at previous cyberattacks, observing the patterns and ways they have affected companies, and coming up with a plan on how to address it in case something similar hits.
Here are some of the major attacks that threatened PH businesses:
ILOVEYOU virus
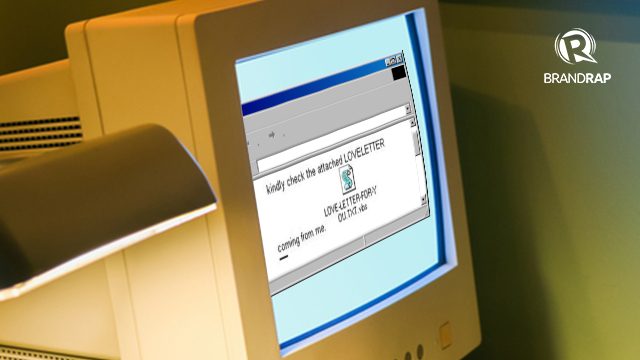
On May 4 to 5, 2000, millions of computers worldwide — including some from The Pentagon and British Parliament — caught the Love Bug after receiving an e-mail with a seemingly harmless subject: ILOVEYOU.
This computer worm, reportedly created by a couple of Filipino IT students, destroyed files and stole user passwords, compromising confidential data from government agencies and private companies.
It spread mainly through corporate email accounts, using address lists so it looked like it came from someone you know. The affected organizations suffered from billions in losses due to unproductivity.
“Comeleaks”
During the 2016 national elections, Comelec became a target of a major cyberattack. Hacker group LulzSec Pilipinas executed what was considered as the biggest leak of private data in Philippine history, endangering over 70 million registered voter records, both active and deactivated.
Criminals could have used (and can still use) the leaked data to access accounts, to blackmail, or to conduct Business Email Compromise (BEC) schemes — a cyberattack in which high-level business executives are impersonated to illegally transfer funds from businesses into the hackers’ account.
Bangladesh bank heist

In February 2016, hackers illegally accessed the credentials of the central bank of Bangladesh to authorize the online transfer of USD 101 million. USD 81 million was sent to the Philippines and was funneled into a leading commercial bank’s foreign currency accounts, and, soon after, was distributed to three major casinos.
The scandal led to a PHP 1 billion fine on the bank and the resignation of its president.
WannaCry
Just last year, WannaCry, a form of ransomware, locked 200,000 computers in 150 countries. The perpetrators demanded USD 300 in ransom to free the encrypted computers.
Although there were no reported victims in the Philippines, this served as a wake-up call as organizations aside from the DICT, like the Bangko Sentral ng Pilipinas (BSP) and Microsoft started taking an active role in preparing businesses, institutions, and the public in case of attacks.
New technologies, new risks
But as we venture into a more connected world, with the dawn of artificial intelligence (AI) and the “Internet of Things”, cyberattacks are becoming more sophisticated while our systems, easier to infiltrate.
We carry Siri in our phones and welcome Alexa into our homes and offices. These intelligent personal assistants know us – where we are, what we want, what we do. They can make decisions for us.
Our houses and offices are synced to computers, our cars are interacting with our mobile phones. Many of these smart devices have no built-in security. And as experts see it, they could just be the hackers’ next big target.
And while steps are being taken to tighten the local cybersecurity,(e.g., banks moving to EMV chips, the DICT formulating a national security framework), technology is just growing faster than the systems in place for protection.
So, if organization leaders and decision-makers don’t start seeking the help of experts and taking concrete steps to protect businesses and stakeholders from looming threats soon, companies are becoming more vulnerable by the minute.
Protecting yourself from cyberattacks
59% of organizations in Asia experience cybersecurity breaches at least once a month. Hundreds of companies, both big and small, have dealt with cyberattacks that have compromised confidential information and resulted in major financial losses.
Encrypting company data and having a strong firewall are some of the initial steps businesses can take. But more importantly, company leaders must take a proactive approach and embrace security as continuous process by investing in the right technology, systems, and in-house cybersecurity experts.
Know more about how you can protect yourself and your business in the upcoming PROTECT 2018 happening on March 12-13 at the New World Hotel in Makati. Check out the full programme here.

PROTECT 2018 is an annual conference that provides a space for dialogue and shared learning between company leaders, government agencies, and other stakeholders in the area of security. There will be exhibits as well where business leaders can check out the security services and products offered by PROTECT partners.
This year’s conference will tackle security threats ranging from man-made (terrorist attacks) to natural (typhoons and earthquakes) with a focus on the future of cybersecurity. Experts from FireEye, Microsoft, Oracle, SYKES, National Privacy Commission, and Booz Allen Hamilton will teach you how to future-proof your business from potential threats.
We are all vulnerable to cyberattacks, but if we are equipped with the right knowledge and tools, we have the power to protect ourselves and our future. — Rappler.com
Add a comment
How does this make you feel?
There are no comments yet. Add your comment to start the conversation.