SUMMARY
This is AI generated summarization, which may have errors. For context, always refer to the full article.
MANILA, Philippines – While the cybersecurity landscape has greatly evolved, most especially with global, highly organized ransomware-as-a-service threats having emerged in recent years, the most exploited point-of-vulnerability among organizations remains an old one: e-mails.
Fortinet manager for systems engineering in the Philippines Nap Castillo said, at the cybersecurity firm’s annual Accelerate conference held on Tuesday, May 31, that “the main attack vector is still the email [containing] malicious links embedded in the email as well as malicious attachments.”
“The threat actors are becoming more innovative [in sending] phishing emails, which are legitimate-looking emails that contain malicious links, and use creative ways of luring the recipient to click on the malicious links. And this is where the magic happens – all of the threats that can be thrown at your endpoint or workstation will happen [once the links are clicked].”
Fortinet VP for marketing and communications in Asia Rashish Pandey acknowledged that the digital landscape now does provide many points at which an attack can begin, but reiterated that email remains to be the most effective. “And email is just one attack vector. You’ve got your network edges. You’ve got your work-from-home edges. The fact that these edges are proliferating, it just provides so many more avenues for a threat actor to come in. But individuals making a mistake, and clicking on links is still probably the most likely way that threat actors get in.”
“Edges” in computer networking can refer to user endpoints such as an employee using a device at home to log in to work applications used by their organization.
Castillo said some of the solutions they provide to organizations include a security application that prevents malicious emails from reaching the end users in the first place, to prevent the exploitation of the weakest link, which is the human; and another one called “FortiPhish,” which is a cloud-delivered phishing simulation service that actually sends fake, harmless phishing emails to users that serve “as a test and as a reminder that these kinds of emails are present” in order to train them and warn them that they are falling prey to phishing.
Pandey expounded on a multi-layered security approach that monitors attacks at every step.
“You have to plan. You’ll never be 100%. But the way for you to think about it is, how will I prevent threats from reaching my organization? If it reaches my organization, how do I prevent them from reaching my users? If they reach my users, how will I prevent [the threat] from getting activated? If they’ve gotten activated, how can we quarantine or limit the amount of damage it has? Once it’s done, how do we learn and update our system [so] that it doesn’t happen again? So you go through the whole cycle, end-to-end. And that’s how you factor in the fact that look, somebody will always click a link.”
“And that’s why it’s important to have that platform view, that it’s not just one solution, not just an email solution. It’s a solution that factors in scenarios, covering a whole range of options,” Pandey said.
Ransomware had an increase of about 11 times over the pandemic compared to pre-pandemic times. The work-from-home setup during the pandemic, Fortinet says, has only contributed to more potential vulnerabilities, due to the use of devices not merely designated for work or provided by the company, leading to potential entry into the organization’s systems.
Sophos, another cybersecurity firm, reported that about 69% of Philippine organizations experienced a ransomware attack in 2021, increasing from 42% back in 2020. The average ransomware payment made by organizations in the Philippines in 2021 was $1.6 million, which was about double the global average.
Cybersecurity professionals needed
Fortinet Philippines country manager Louie Castañeda also addressed the lack of cybersecurity professionals needed to keep up with current demand. Before the pandemic, it was estimated that, worldwide, that there was a deficiency of about 2 million cybersecurity professionals needed – a number, which the company says, has only increased during the pandemic.
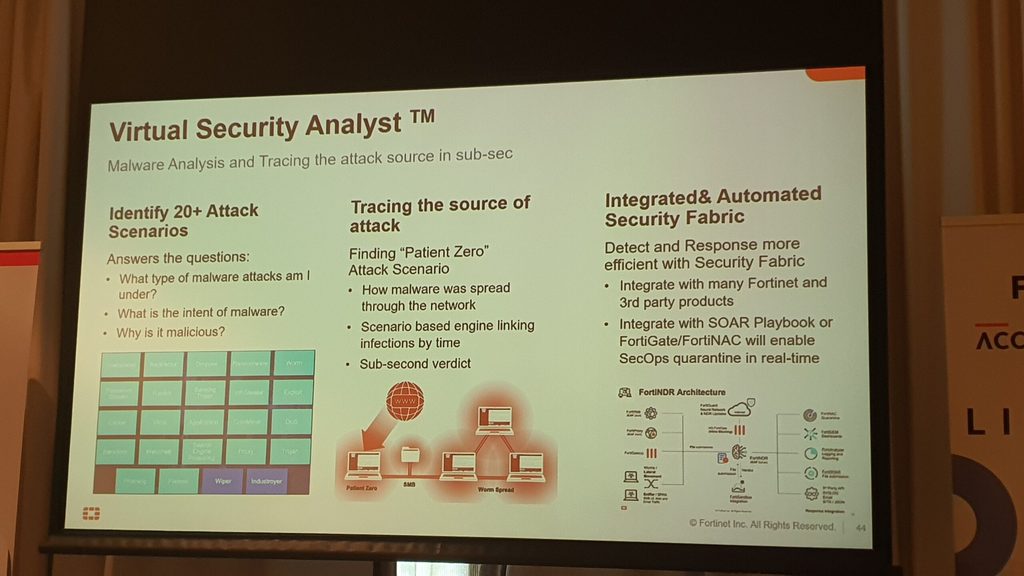
While the company makes use of AI and machine learning in its products to help it adapt quicker to threats, the hybrid human-AI model approach applies in the field of cybersecurity as well. Human talents are needed to keep up with threat groups, which themselves can also make use of AI-powered automation techniques to conduct attacks.
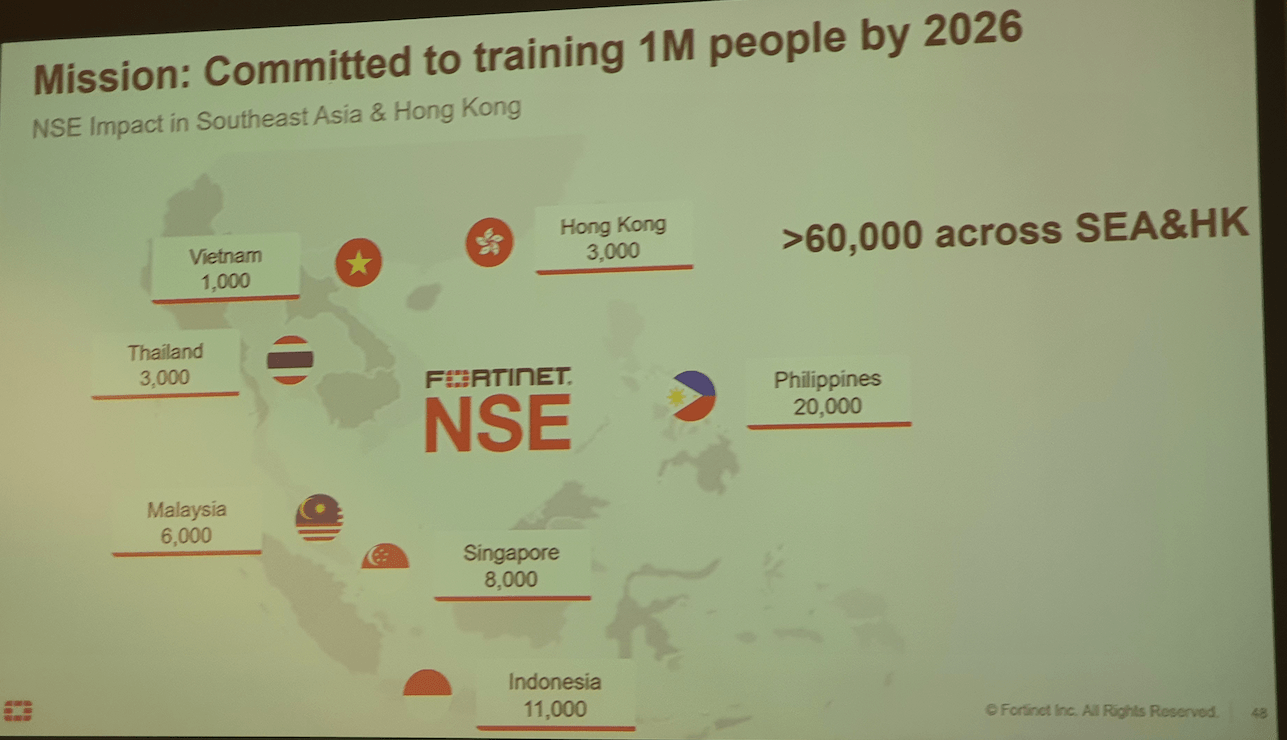
Fortinet says, through their programs – which also includes reaching out to kids through a children’s book on the importance of cybersecurity – they’ve assisted about 20,000 people in the Philippines to become certified as a Network Security Expert (NSE). It’s the highest number of people they’ve assisted in the Southeast Asia region, yet a large number of cybersecurity openings remain not only in the Philippines but worldwide.
Currently, the two most in-demand cybersecurity positions are the security operations center (SOC) analyst, which monitors and fights against cyber threats, and cloud security specialist, according to the firm. And to help out human talents, Fortinet stressed that services provided by cybersecurity firms need to be comprehensive and streamlined so a professional such as the security operations center analyst need only monitor threats using applications from one or a few vendors rather than many vendors.
And how much can aspiring SOC analysts potentially earn? It could be a lucrative trade, with estimates putting it at about $100,000 per annum internationally. Not bad for a life of fighting cybercrime. – Rappler.com
Add a comment
How does this make you feel?
There are no comments yet. Add your comment to start the conversation.