SUMMARY
This is AI generated summarization, which may have errors. For context, always refer to the full article.
AT A GLANCE
- One member of Pinoy Vendetta, a hacking group known for conducting DDoS attacks against critical media and praised by the NTF-ELCAC for attacks on the website of the Communist Party of the Philippines, has been identified.
- The hacker is described as in his 30s and a former information technology student in Davao.
- The hacker earlier claimed he had left the group a little over two weeks before the first attack began in June 2021 but was seen again in July 2021 posting on a Pinoy Vendetta-linked page (www.facebook.com/PV.Dr3inuS.Official/) about the website of the game Axie Infinity being down.
- Numerous attempts to make contact with the hacker have been made but the hacker has been evasive, and has not answered questions directly. When reaching out to him on Facebook on his various accounts, his reactions would be to either deactivate the page or block us shortly after receiving the message, or just leave a message as seen. We have only been successful once in getting a statement from him, made possible through a relative. He has likewise ignored all attempts by digital forensics non-profit Qurium Media to reach out to him.
- Numerous social media accounts and other online properties linked to the hacker started to disappear or be renamed after our initial February 24 article on Pinoy Vendetta’s DDoS attacks.
MANILA, Philippines – Sweden-based digital forensics non-profit Qurium Media, in a blog post dated March 9, identified one of the members of the hacking group that had been conducting DDoS attacks on news websites that included ABS-CBN, CNN Philippines, and Rappler. These attacks also hit certain opposition politicians such as Leni Robredo, through the Office of the Vice President website, Dick Gordon, and Leila de Lima.
DDoS attacks flood websites with fake traffic to bring them down. They are a form of interference that is illegal according to the Philippines’ e-commerce law enacted in 2000. Since its enactment, however, no one in the Philippines has been punished or jailed for launching DDoS attacks due to the difficulties in tracing actors digitally.
Worldwide though, there have been several arrests made. In the Netherlands, an 18-year-old turned himself in to the victim organization, Bunq bank, after he became a suspect, thanks to IP address and attack pattern analyses, along with chatter in IT communities.
Earlier in 2016, 34 suspects were arrested by an international police operation, including teenagers. “DDoS tools are among the many specialized cyber-crime services available for hire that may be used by professional criminals and novices alike,” BBC quoted Steve Kelly, unit chief of the FBI’s International Cyber Crime Coordination Cell.
The Pinoy Vendetta member had been described as in his 30s and said to be a former information technology student of the Davao Merchant Marine Academy College of Southern Philippines.
Online and social media activity collected by Qurium links the hacker with the aliases Shin Takata, Dreinus/Dr3inuS, Pure Filipino/4tt4ck30n3, Kali Shin, shinigami192, Yoshimura192, shint4k4t4, and Crtc4l/Crtc4L. Among the evidence collected by Qurium, and later verified by Rappler, was the domain crtc4L.com, whose domain registry records show ownership by the hacker.
On Facebook, several results appear when searching Shin Takata, but the hacker’s Facebook account is under the address www.facebook.com/shintakata4124 (inactive). Other platforms where the hacker used the Shin Takata alias include www.instagram.com/shint4k4t4/ (inactive), www.pinterest.com/yoshimura192/ (active), www.github.com/shinTakata (now renamed to github.com/ChakriWongsuwon, and is active), and on a channel on chat app Discord, among others.
From 2019 to 2020, the hacker using another one of his aliases, Crtc4L, was the most visible member of Pinoy Vendetta on its Facebook page, signing nearly all of the posts during that time period with that specific alias. The hacker’s posts were mostly about cybersecurity issues, but from time to time, they indicated a pro-Duterte stance, taking potshots at opposition figures and government critics.
What is the Qurium Media Foundation?
The Qurium Media Foundation, which works with independent media and investigative journalists around the world, was officially founded in February 2014, but its history can be traced back to 2009, according to its history page. The foundation provides digital forensics investigations on “Internet censorship, targeted malware, disinformation campaigns, election fraud, digital attacks against media sites, and other digital threats against a free and open Internet.”
In the Philippines, prior to their work identifying a Pinoy Vendetta member, they had conducted DDoS investigations on attacks targeted at alternative news sites and human rights organizations such as Bulatlat, Altermidya, and Karapatan, and made its loudest headlines in the Philippines when the group found some traces linking certain machines in DDoS attacks to the Philippine military and the Department of Science and Technology (DOST).
The army denied the allegations but the IP address found in the attack was confirmed by the Department of Information and Communications Technology’s (DICT) Computer Emergency Response Team to have been assigned to the AFP.
The DOST also denied links to the DDoS attacks, and Qurium – in communications with the department – said they were told that “they (DOST) just [assisted] other government agencies by allowing the use of some of its IP addresses in the local networks of other government agencies.” Qurium’s history of published forensic work can be found here.
Crtc4L’s posting history on Pinoy Vendetta
In March 2019, Crtc4L called ABS-CBN biased, and deemed the station unworthy of being granted a new license to operate. The network’s franchise was set to expire in March 2020. The House committee on legislative franchises later rejected the network’s application in July 2020.
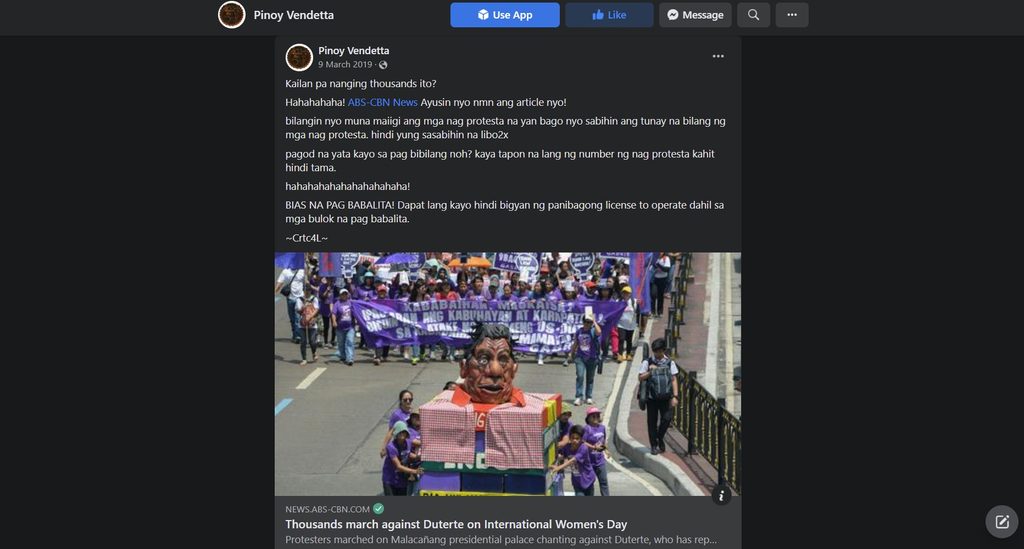
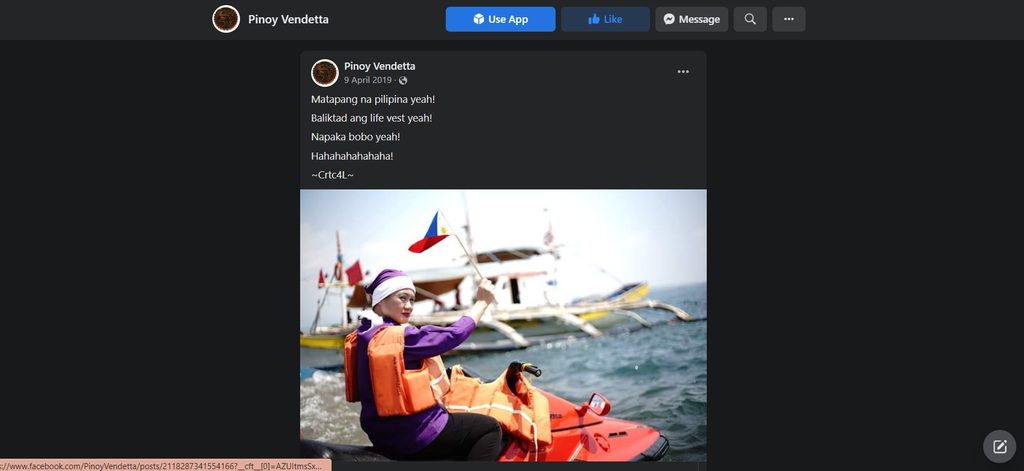
Crtc4L also mocked then-opposition senatorial candidate Samira Gutoc for wearing a life vest backwards in April 2019.
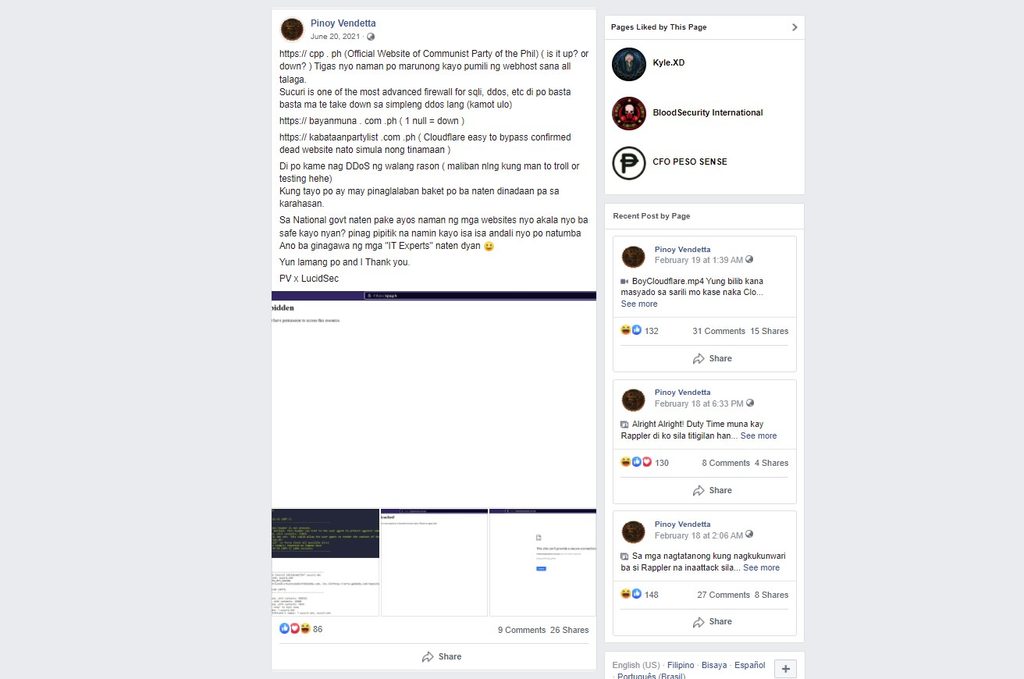
In July 2020, the hacker also attacked the Communist Party of the Philippines (CPP), calling the developer of their website, CPP.ph, “pulpol” (dumb).
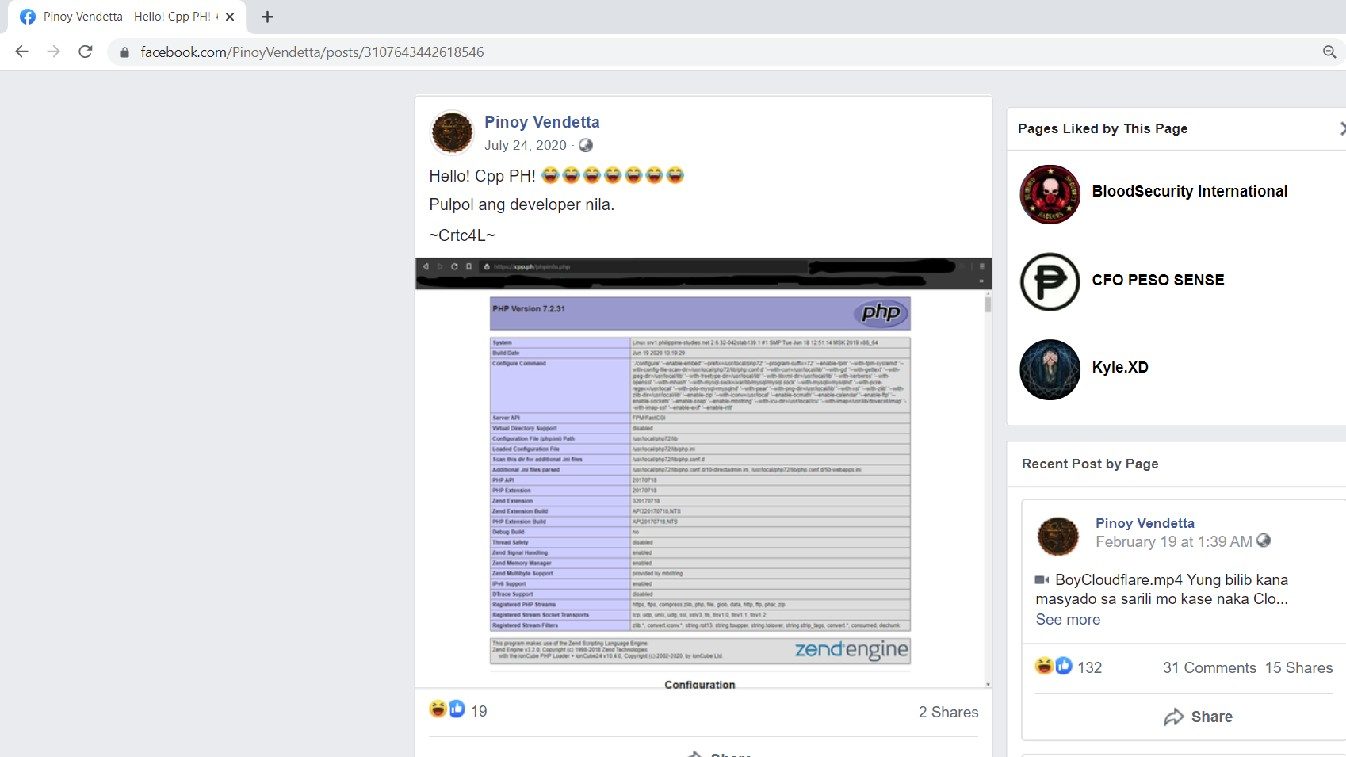
The CPP would become a primary target of the group in 2021, and this “achievement” would later earn it praise from the National Task Force to End Local Communist Armed Conflict (NTF-ELCAC) and its spokesperson Lorraine Badoy.
Throughout 2020, several other posts on the Pinoy Vendetta page signed by Crtc4L took aim at Pinoy Ako Blog, a website critical of the Duterte administration, as well as activists on TikTok who wanted to junk the anti-terror bill, and people speaking out against the ABS-CBN shutdown.
In the first half of 2021, posts were less frequent on the Pinoy Vendetta page compared to 2020. But on May 28, 2021, Critc4L returned with a post saying: “Hello! kumusta kayo? sorry hindi ako naka post dito sa sobrang busy” (How are you? Sorry I haven’t been posting here because I’ve been so busy.)
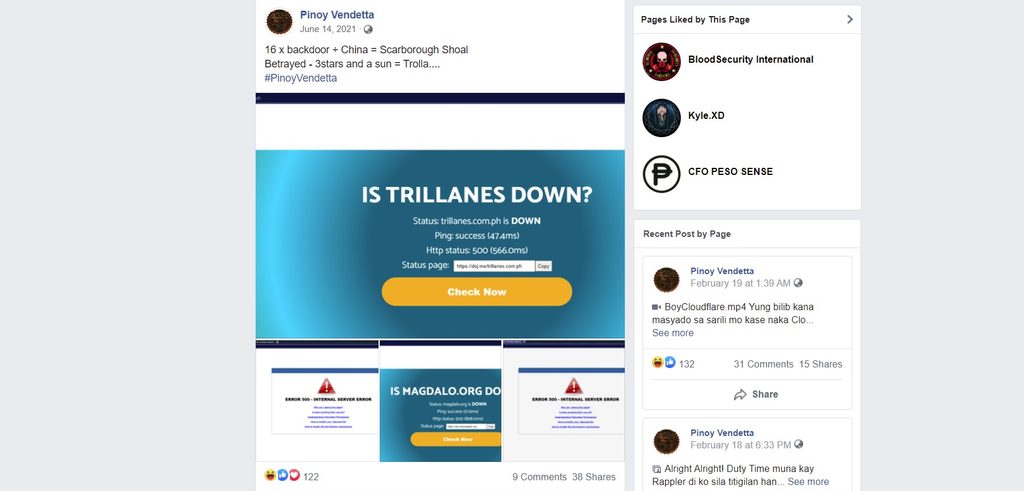
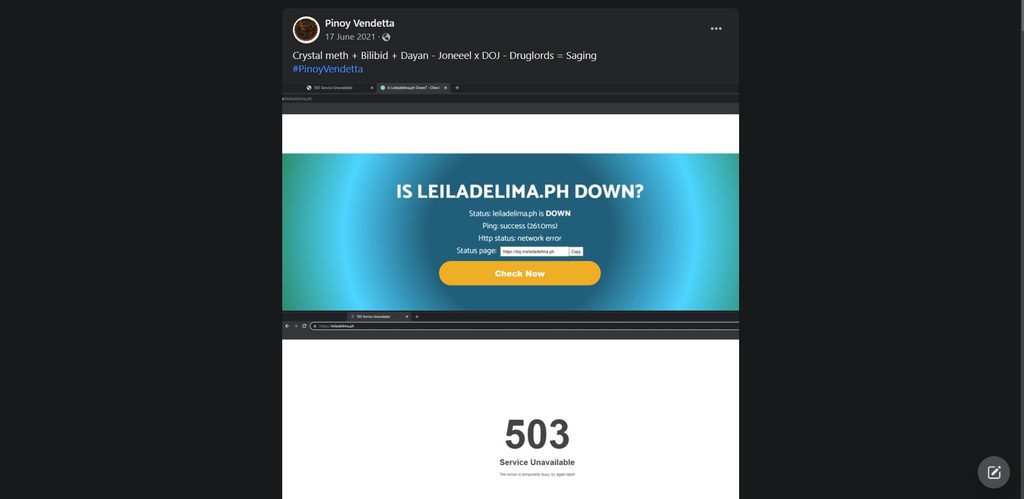
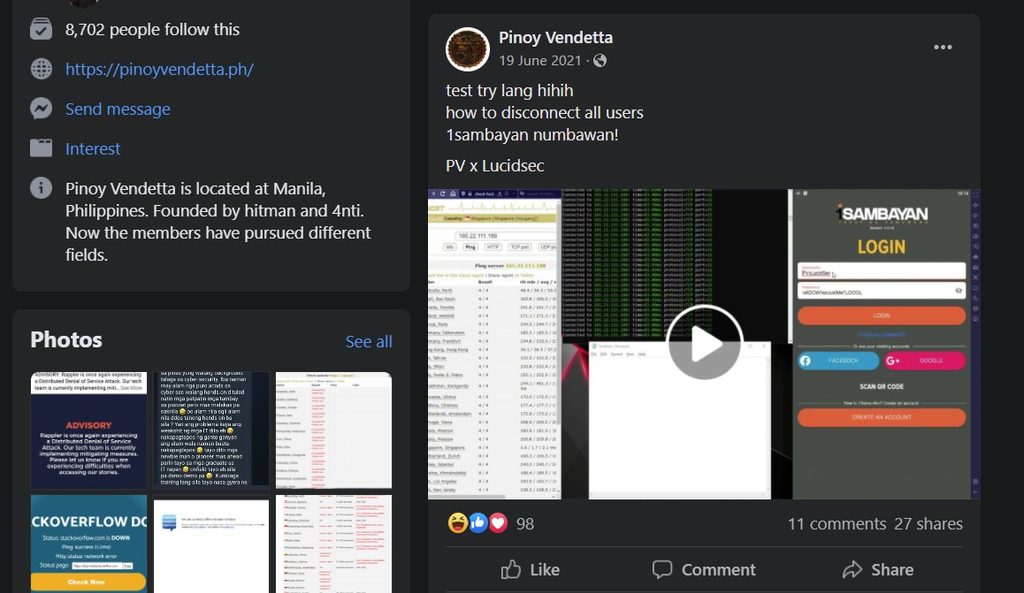
Just a little over two weeks after Crtc4L’s post, the first series of attacks in 2021 claimed by Pinoy Vendetta began including the website of former senator Antonio Trillanes, trillanes.com.ph, on June 14; the website of Senator Leila de Lima on June 17; the website of opposition coalition 1Sambayan on June 19; and the CPP.ph website on June 20. Screenshots of these attacks are shown below:
At this point, none of the attacks were specifically signed by Crtc4L.
Reaching out to the hacker
We began reaching out to the hacker about a week before the publication of an earlier article on the Pinoy Vendetta DDoS attacks on February 24 through email. Later, we reached out to his accounts on Facebook, Shin Takata (www.facebook.com/shintakata4124), and Shin Gaming (www.facebook.com/CyberShinGaming).
On the Shin Takata Facebook page, we received one reply: “sino to?” (who’s this?) on February 20. We were able to send one last reply on Monday, February 21, before he shortly made his account inaccessible, and unreachable via Messenger:
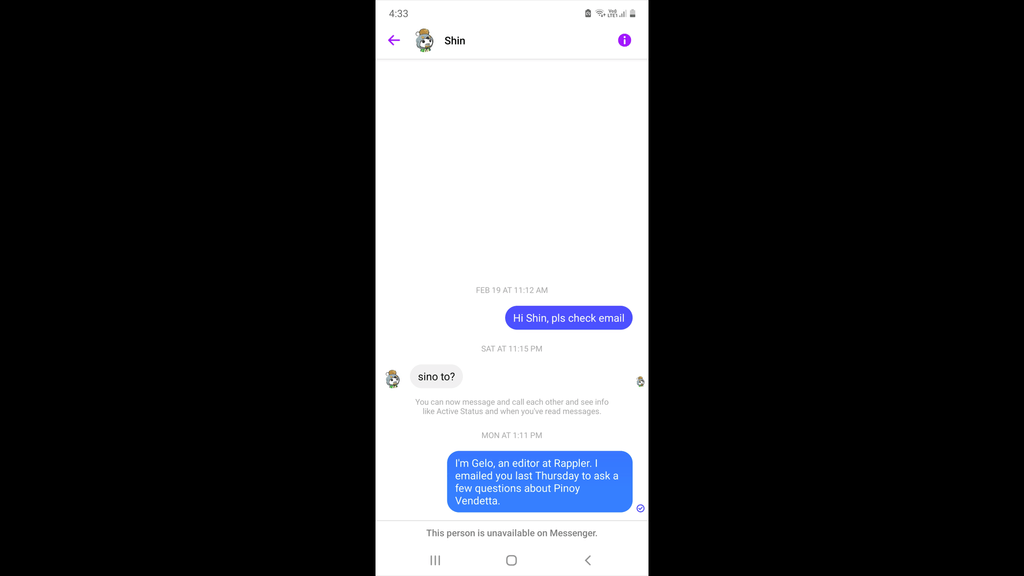
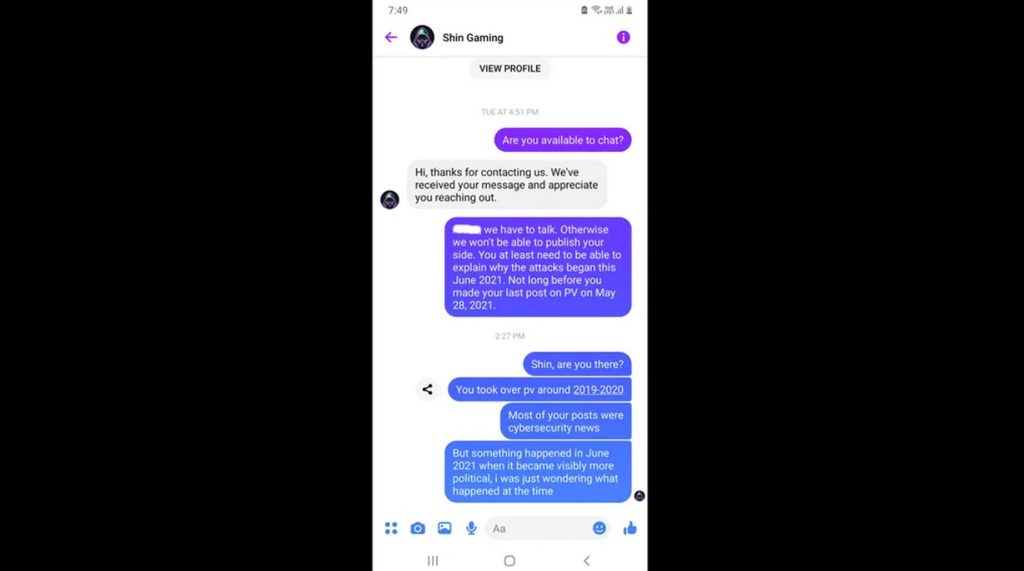
We followed up with a message to the hacker’s Shin Gaming account on Tuesday, February 22, where he saw our message and ignored it.
Unable to reach him through his accounts, we sent a message to a relative of his on February 23, asking if we could be connected.
We received a message from the hacker through his relative on February 24, a few hours after our first Pinoy Vendetta article came out.
In verbatim, he said: “Hello gelo i saw your article. And i have no connection to the group because i just left that group after my last post and i never. I did not do any of these attack on the website. I’m not the only one handling the page. I do not know who are they and where they live. I just share any weakness of a site and not to disrupt it. The attacks on the news is not work of mine but the others. Sorry for late reply. Please remove my code name and the connection to the group because i am no longer member of them.”
A separate Pinoy Vendetta page that appeared after the original one (previously located at facebook.com/PinoyVendetta) was taken down shared the Rappler February 24 article, stating that the article was pinning the blame on a person who left the page a long time ago.
“Tapos pinagbibintangan pa mga taong matagal ng wala sa page; [kung sa bagay] mga dummies account lang ‘yan.” (Then they’re pinning the blame on people who left a long time ago; in any case they’re only dummy accounts.) The screenshot is below:
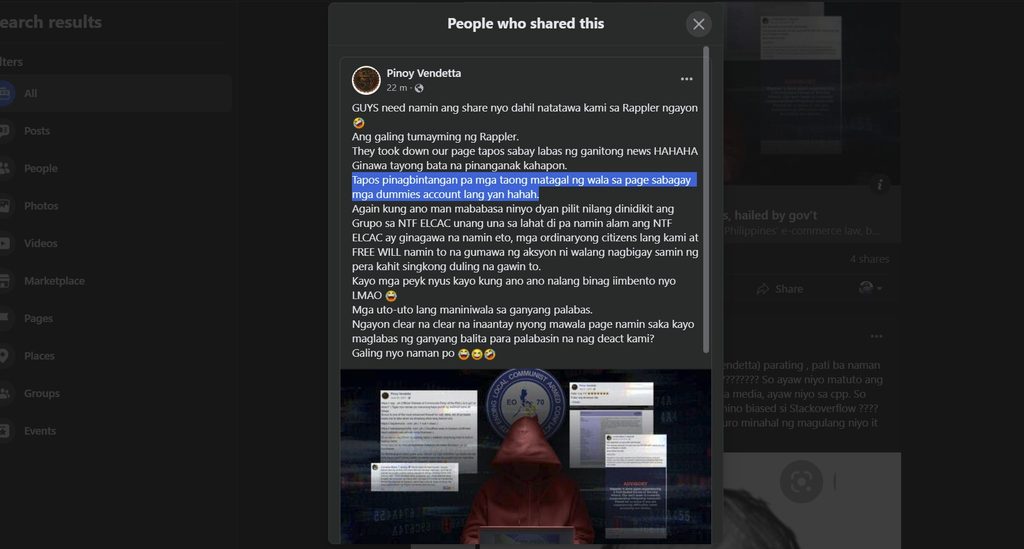
The statement followed the hacker’s claim that he had already left the group.
Pinoy Vendetta then took down the original post, and reposted it or edited the text, removing the part that imputed the hacker’s involvement with the group:
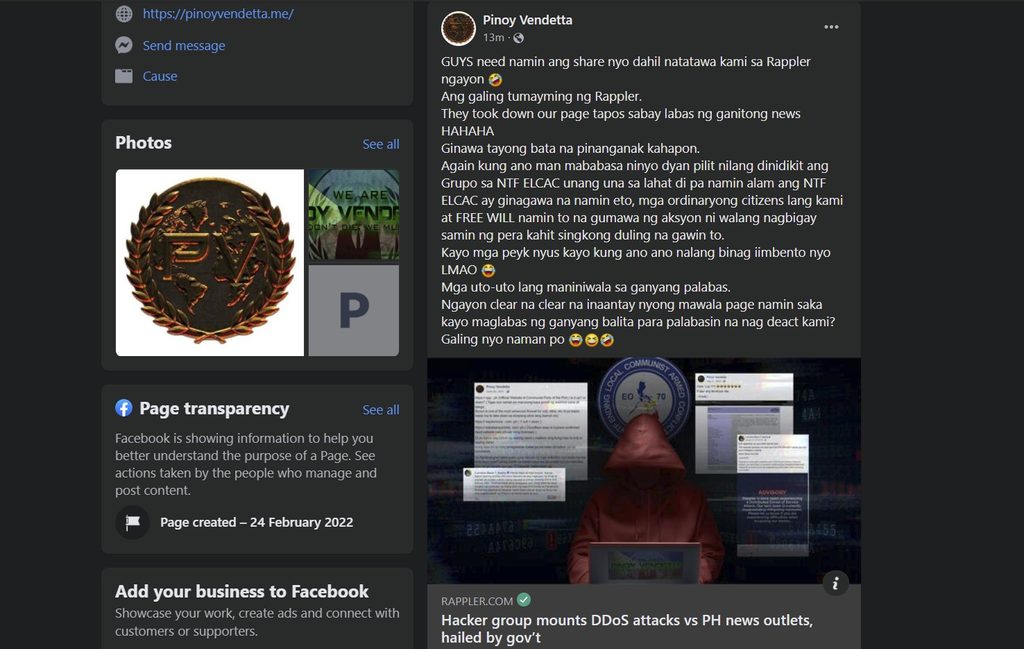
The group also admitted that they had been doing cyber attacks before they even knew what the NTF-ELCAC was. “Unang-una sa lahat ‘di pa namin alam ang NTF ELCAC ay ginagawa na namin ito.” (First of all, we’ve been doing these attacks even before we knew about the NTF ELCAC.) Had the hacker been involved in those earlier attacks that the group is claiming credit for?
Social media pages and other online properties linked to the hacker – shown on a list at the bottom of this article – also started to disappear or be renamed after the publication of the February 24 article.
Contradictory statements
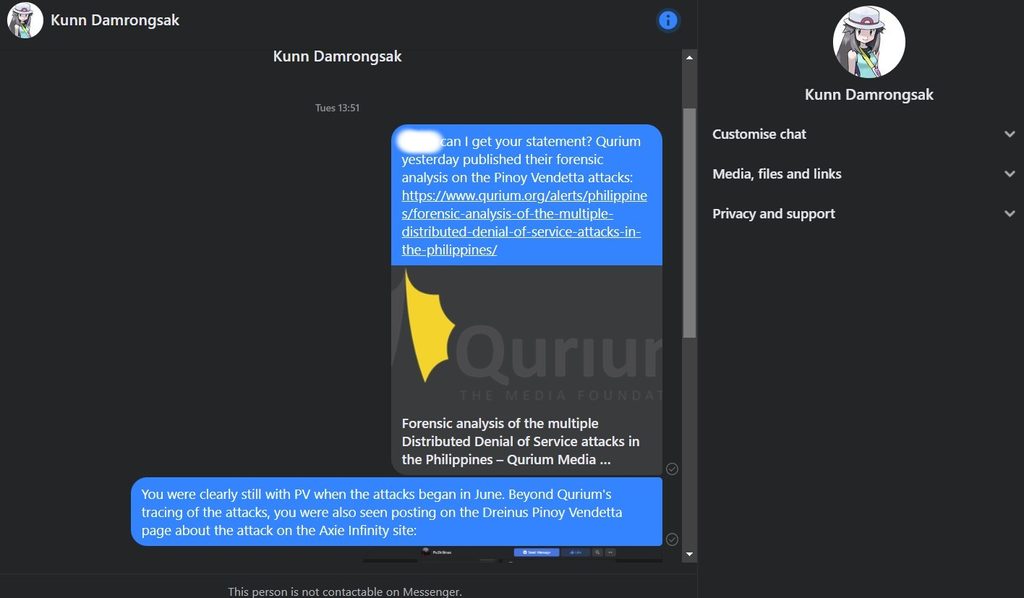
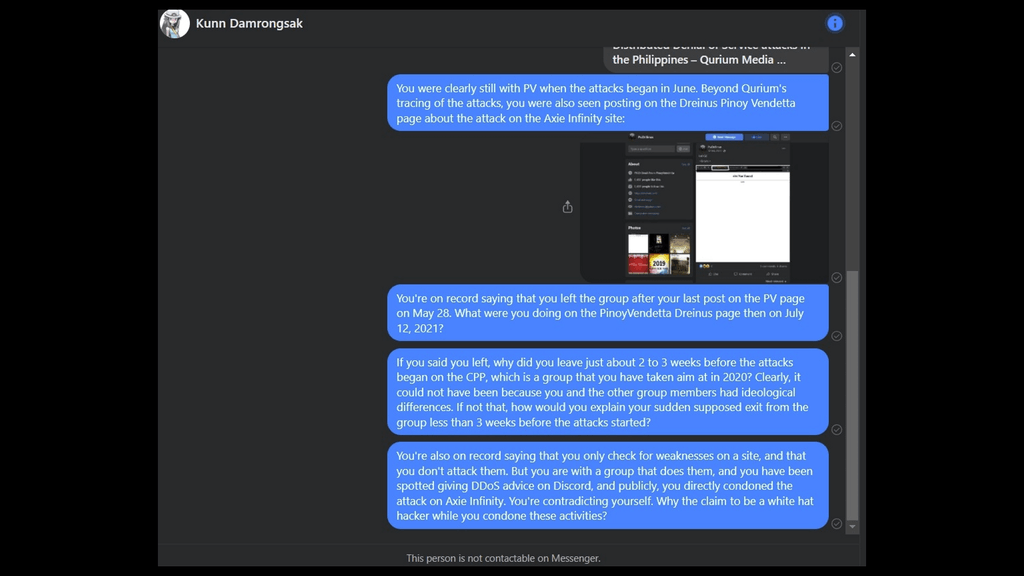
While the hacker denied still being part of Pinoy Vendetta after May 28 – a group that has become a cyber gang conducting criminal DDoS attacks – a July 12 post on a Pinoy Vendetta-linked page (www.facebook.com/PV.Dr3inuS.Official/) shows otherwise.
The hacker on July 12, 2021 – signing as Crtc4L on the Pinoy Vendetta Dreinus page – posted about the website of the game Axie Infinity being down.
Axie Infinity is one of the most popular blockchain-based games today, with monthly active users estimated at more than 2.5 million worldwide.

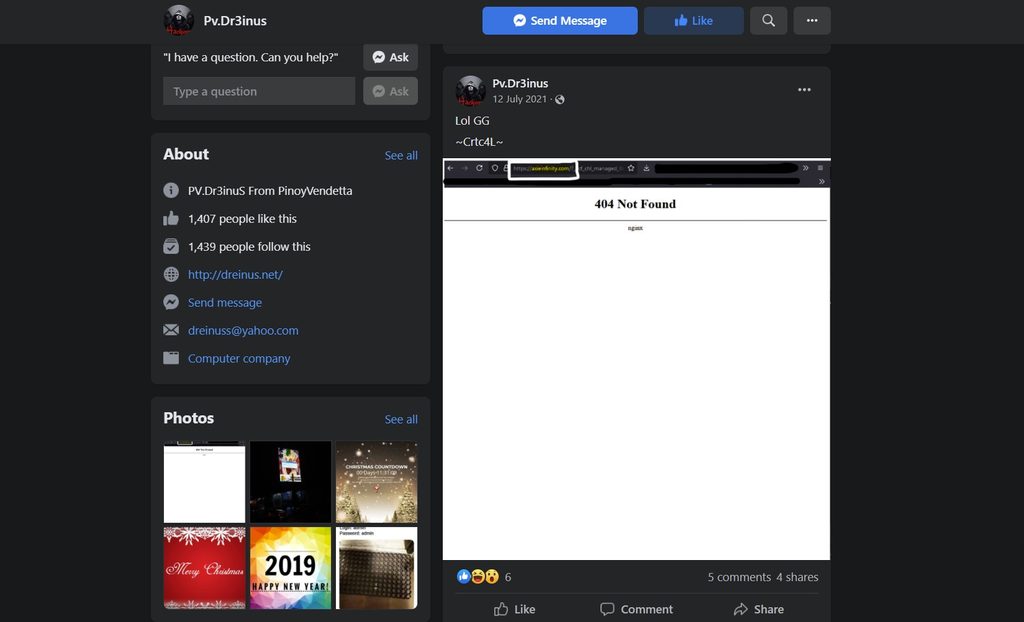
The hacker is also seen in the comments section, shown below, saying, “Na down kagabi pero bumalik agad.” ([The Axie Infinity website] went down last night but it went back up immediately.)
Crtc4L did not explicitly say it was a DDoS attack that had brought the Axie website down nor did he make a claim that Pinoy Vendetta had attacked it. But his post on the Pinoy Vendetta Dreinus page contradicted his claim that he no longer had any involvement with the group after his supposed exit after his final post on May 28 on the main Pinoy Vendetta page (www.facebook.com/PinoyVendetta/).
On July 13, a day after Crtc4L made the post showing the Axie site being down, the official Axie Infinity page on Twitter made the announcement that it was experiencing a DDoS attack.
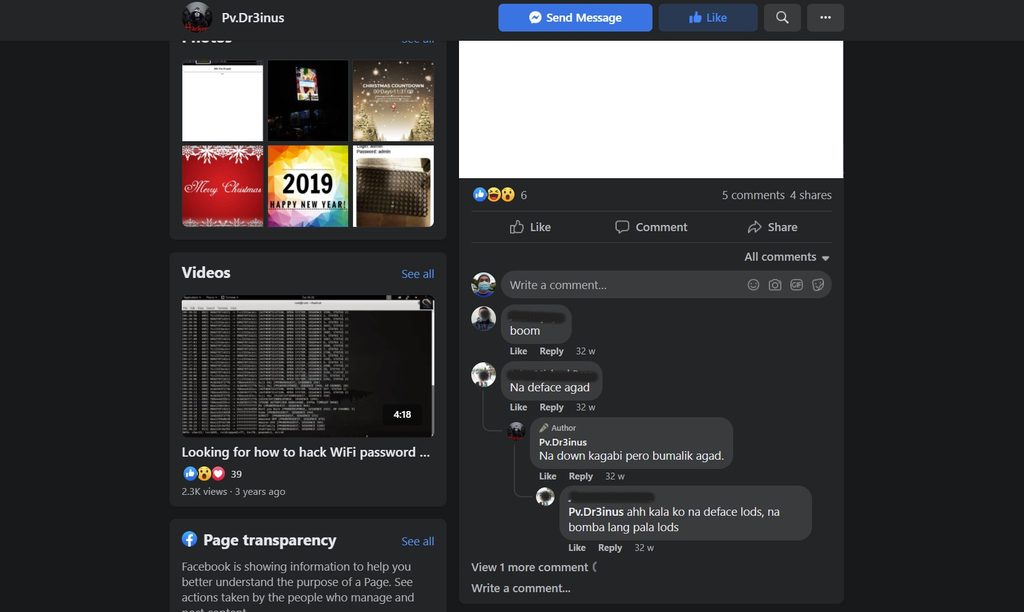
The official Pinoy Vendetta Facebook page also posted about the Axie Infinity website being down, but we were unable to take a screenshot of this post. A few digital traces, however, remain on Google Search:
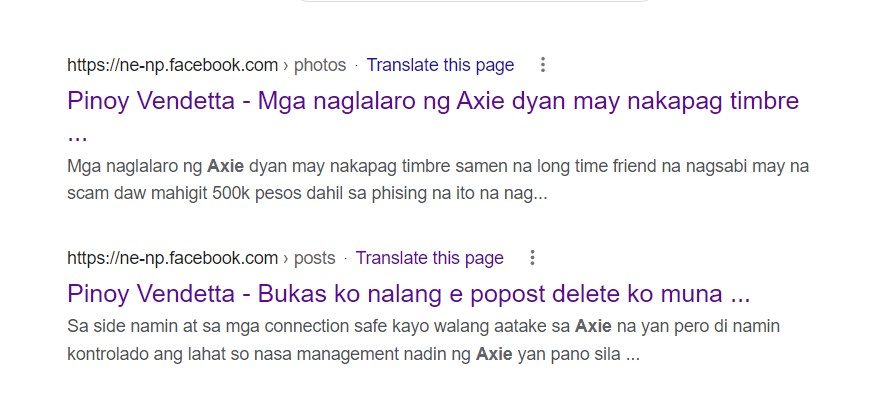
One of the search results shows a text preview of the Facebook post by Pinoy Vendetta saying, “Sa side namin at sa mga connection, safe kayo, walang aatake sa Axie na ‘yan pero ‘di namin kontrolado ang lahat so nasa management narin ng Axie ‘yan pano sila…” (On our side and to our connections, you’re safe, no one’s going to attack Axie. But we don’t control everyone so it’s still up to the management of Axie.)
The post implies there are several Pinoy Vendetta members, and that it’s unclear who among them might launch an attack.
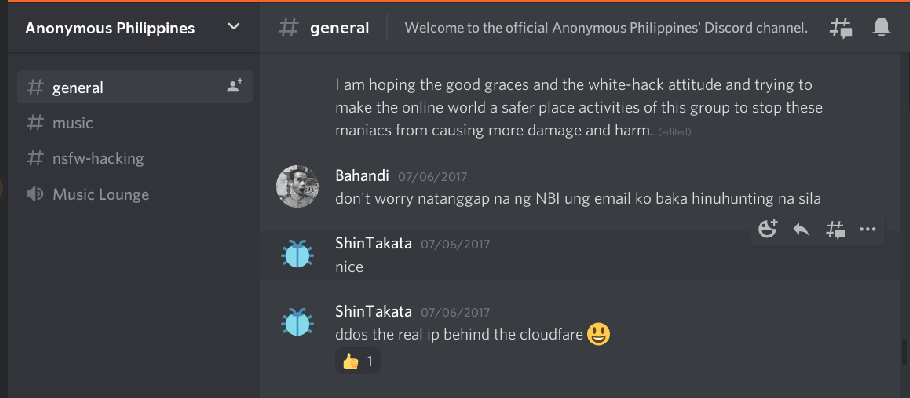
In the channel of hacking group Anonymous Philippines on the messaging app Discord, the hacker this time using his other alias Shin Takata, was also found providing advice about DDoS attacks way back in 2017, as shown below. Qurium said, “While he presents himself as a ‘white hat hacker’ or ‘ethical hacker,’ his promotion of methods such as Denial of Service attacks is highly questionable.”
Completing the hacker’s profile, Qurium had also documented him posting as 4tt4ck3r0n3 on Twitter, and as Crtc4L on e-commerce platform Rocketr, selling proxies.
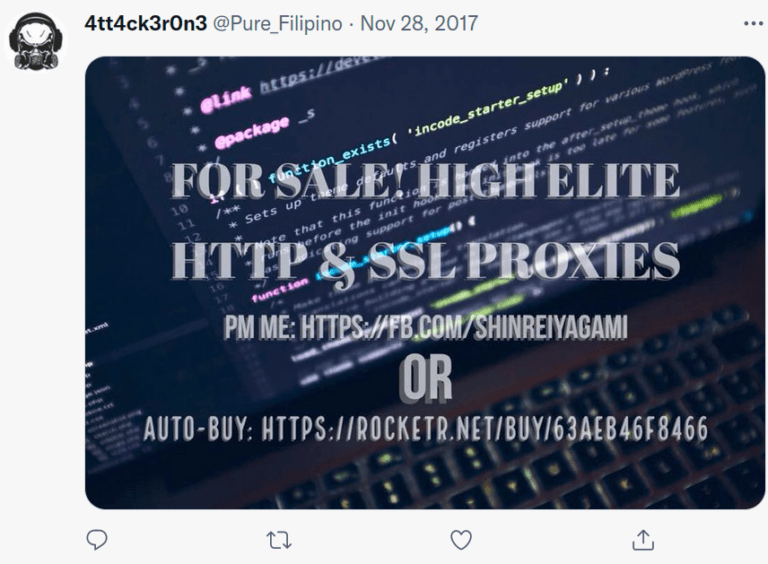
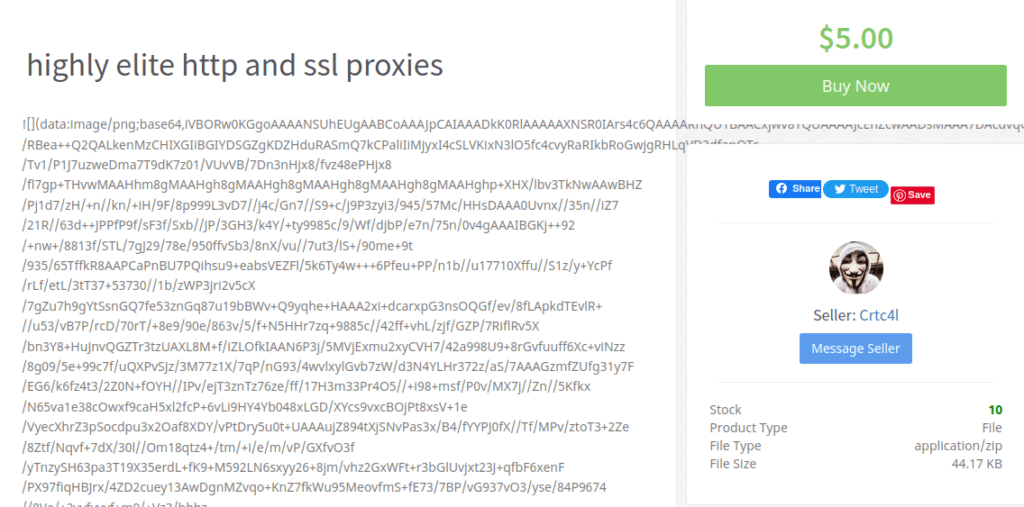
Proxies or proxy servers can be used to anonymize one’s activities online or to bypass certain geo-restrictions. But these could also be used for black-hat search engine optimization (SEO) creating fake traffic to create revenue for websites, and for DDoS attacks. “In fact, the PV_RAW DDoS tool used by Pinoy Vendetta uses proxies to initiate the attacks,” Qurium told Rappler.
Still no response
On Tuesday, March 15, we sought out the hacker once again to get his comment on the Qurium report that had identified him, and to ask for further details on his claimed exit from the group just a little over two weeks before the first DDoS attacks claimed by Pinoy Vendetta began. We also sought an explanation about his continued posting on the Pinoy Vendetta Dreinus page in July 2021 when his initial statement said he left right after he made his last post on May 28, 2021.
The messages were sent to another one of the hacker’s Facebook accounts under the Thai name of Chakri Wongsuwon (www.facebook.com/chakrii2789/) which is also another one of the hacker’s aliases. About two hours after sending the message to the account, the hacker once again deactivated the page – as had been the case when we sent him a message back in February on his Shin Takata account – and made it unreachable via Messenger. The page was also then renamed using another alias Kunn Damrongsak (www.facebook.com/chakrii2789/). As of publication time, the page remained inaccessible.
The hacker has also consistently evaded emails from Qurium. “During the past weeks, Qurium has tried to reach [name redacted] a number of times, asking for an explanation. To our surprise, [name redacted] never returned our emails. However, after receiving our emails, he immediately deleted all evidence in his multiple social media accounts (Facebook, Github, Instagram),” Qurium said.
The Chakri Wongsuwon/Kunn Damrongsak page is the latest one (associated with the hacker and Pinoy Vendetta) to have been deactivated, according to a list by Qurium. The list includes the availability status of the pages:
- www.facebook.com/shintakata4124/ (inaccessible)
- www.facebook.com/Crtc4L/ (inaccessible)
- www.facebook.com/chakrii2789/ (inaccessible)
- www.facebook.com/PinoyVendetta/ (removed by Facebook)
- www.facebook.com/PinoyVendetta.Official/ (removed by Facebook)
- www.facebook.com/pv.theordinarycitizens/ (inaccessible)
- www.github.com/shinTakata renamed to github.com/ChakriWongsuwon
- www.twitter.com/t4kish4m4 (inaccessible)
- www.twitter.com/Pure_filipino (inaccessible)
- www.facebook.com/pinoycyberddos (inaccessible)
- www.instagram.com/kali_shin/ (active)
- www.instagram.com/shint4k4t4/ (inaccessible)
- www.instagram.com/ch4krii/ (inaccessible)
- www.facebook.com/PV.Dr3inuS.Official/ (inaccessible)
- www.facebook.com/CyberShinGaming renamed to www.facebook.com/newlocalhost (active)
- www.pinterest.com/yoshimura192/ (active)
- www.tiktok.com/@chakriwongsuwon (active)
- www.pinterest.com/shinrei192/ (active)
- www.facebook.com/CuteGirlsOfPhilippines (inaccessible)
- www.verycutegirlsinjapan.wordpress.com/ (active)
- www.flickr.com/photos/cutegirlsofjapan/ (active)
- www.facebook.com/ddos.PHU.edu.ph/ (inaccessible)
Among these pages, Facebook owner Meta confirmed on March 2 that www.facebook.com/PinoyVendetta had been officially taken down. Two new Pinoy Vendetta pages were created after but were also taken down shortly. A Meta spokesperson told Rappler: “The pages have been removed from Facebook for repeatedly violating our policies.”
We last reached out to the hacker’s relative again on Wednesday, March 16, to seek his comment, and as of Wednesday, April 6, have not received any response. We will update this story once we get one. – Rappler.com
Add a comment
How does this make you feel?
There are no comments yet. Add your comment to start the conversation.